eBPF
eBPF (extended Berkeley Packet Filter) is a technology that allows you to write custom programs that can be attached to various points in the Linux kernel. These programs are called eBPF programs, and they run in a secure environment inside the kernel.
eBPF was originally designed as a way to implement custom packet filters in the Linux kernel, but it has since evolved into a more general-purpose technology that can be used for a wide range of tasks, including networking, security, tracing, and performance analysis.
eBPF programs are written in a subset of the C programming language, and they are compiled into a bytecode format that can be loaded into the kernel. Once loaded, an eBPF program can be attached to a specific kernel function or data structure, such as a packet filter, a system call, or a kernel tracepoint.
eBPF has become a powerful and widely used tool in the Linux ecosystem, and it is supported by many tools and libraries, including the Linux perf tool, the bcc (BPF Compiler Collection), and the Linux kernel’s tracing infrastructure.
eBPF is an extremely flexible technology that can be used in a wide range of contexts, and it is a valuable tool for anyone who works with Linux systems.
Architecture and components of eBPF
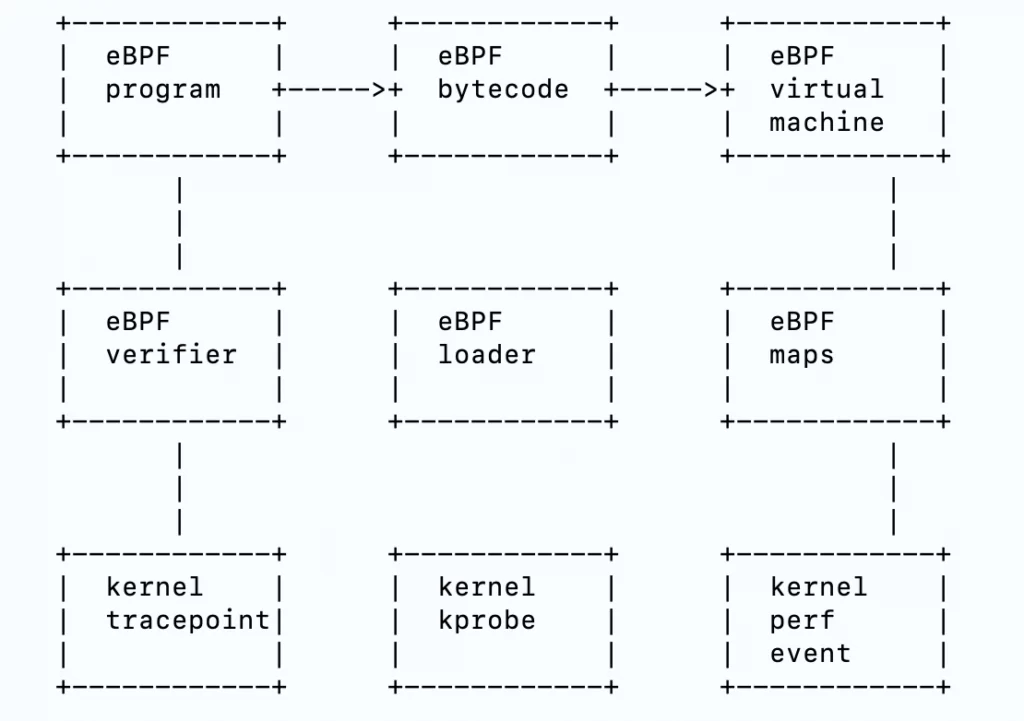
eBPF architecture consists of several components,
- eBPF programs: These are the programs that are written in a subset of the C programming language and compiled into a bytecode format. eBPF programs can be attached to various points in the kernel, such as packet filters, system calls, or trace points.
- eBPF bytecode: This is the compiled form of an eBPF program, which is a sequence of instructions that can be executed by the eBPF virtual machine (eBPF VM).
- eBPF virtual machine (eBPF VM): This is the runtime environment that executes eBPF bytecode. The eBPF VM is implemented in the Linux kernel, and it runs in a secure environment inside the kernel.
- eBPF maps: These are data structures that can be used to store and retrieve data from within an eBPF program. eBPF maps can be used to pass data between eBPF programs or to store data that needs to be accessed by multiple eBPF programs.
- eBPF verifier: This is a static analysis tool that is used to verify the safety and correctness of eBPF programs before they are loaded into the kernel. The eBPF verifier checks the eBPF bytecode for any potential issues, such as memory access violations or infinite loops, and it ensures that the eBPF program adheres to the eBPF sandboxing rules.
- eBPF loader: This is the component that is responsible for loading eBPF programs into the kernel and attaching them to the appropriate kernel functions or data structures. The eBPF loader is responsible for ensuring that the eBPF program is loaded safely and securely, and it manages the lifetime of the eBPF program within the kernel.
- eBPF infrastructure: This includes the various kernel functions and data structures that are used to support eBPF, such as tracepoints, kprobes, and perf events. The eBPF infrastructure provides the hooks and interfaces that eBPF programs can use to interact with the kernel.
Advantage of eBPF
- Performance: eBPF programs run directly in the kernel, which means they can execute much faster than userspace programs. This makes eBPF an ideal choice for tasks that require low latency or high throughputs, such as packet filtering or tracing.
- Security: eBPF programs run in a secure environment inside the kernel, which means they cannot access or modify sensitive kernel data or memory. This makes eBPF an attractive option for tasks that require a high degree of security, such as intrusion detection or network security.
- Flexibility: eBPF programs can be attached to a wide range of kernel functions and data structures, which means they can be used for a wide range of tasks. This makes eBPF a very flexible tool that can be used in many different contexts.
- Ecosystem: eBPF is supported by a large and growing ecosystem of tools and libraries, which makes it easy to develop, debug, and deploy eBPF programs.
- Community: eBPF has a large and active community of developers and users, which means you can find help and support when you need it.
Books on eBPF
Here are a few books that provide in-depth coverage of eBPF,
- “BPF Performance Tools: Linux System and Application Observability” by Brendan Gregg: This book provides a comprehensive guide to using eBPF and other Linux performance tools to analyze and optimize system and application performance.
- “Linux Kernel Networking: Implementation and Theory” by Rami Rosen: This book provides a detailed look at the Linux kernel networking stack, including coverage of eBPF and its role in networking.
- “Linux Kernel Development” by Robert Love: This book is a classic resource for understanding the internals of the Linux kernel, including its use of eBPF.
- “Mastering Linux Kernel Development” by Chris Mason: This book provides a comprehensive guide to developing and debugging the Linux kernel, including coverage of eBPF.
- “Linux System Programming” by Robert Love: This book provides a broad overview of system programming in Linux, including coverage of eBPF and its role in system programming.
In addition to these books, there are many online resources available for learning about eBPF, such as official documentation, tutorials, and blogs.
For more information please visit ebpf.io
This article is created based on experience but If you discover any corrections or enhancements, please write a comment in the comment section or email us at contribute@devopsforu.com. You can also reach out to us from Contact-Us Page.
Follow us on LinkedIn for updates!